Preparing for cyber attack – by John Hines

Skills are top of mind today with a jobs and skills summit in Canberra. With deteriorating relations between Australia and a number of countries a cyber skills shortage is looming large for manufacturers. John Hines outlines what can be done.
The cyber security skills gap in Australia is reaching unprecedented levels. The hunt for talented candidates is hotly contested, and there aren’t nearly enough experienced professionals to fill the number of job openings.
Reports have estimated that nearly 17,000 more cybersecurity workers are needed in Australia by 2026 and that current growth is not sufficient to meet medium-term shortfalls.
Take the Australian government’s huge investments in enhancing the cybersecurity capabilities of the Australian Federal Police and the Australian Signals Directorate, along with the rest of government and private industry’s search for cyber security talent, and you get an idea of how hard it becomes for small-to-medium enterprises to compete
While efforts are underway to start to bridge this gap, these will take time, and while we wait, the cyber threat to Australian businesses continues to grow.
What to look out for?
Even with tight resources and a lack of cyber security-related expertise, there are ways for organisations to help manage this risk.
Resources are available that can be a great start for security practitioners to look for data-driven, real-world views on what commonly befalls companies with regard to cybercrime.
While they won’t solve the current cyber security talent shortage, understanding the most prolific threat actors and actions affecting assets can help inform IT and security teams on where best to focus their resources and effort.
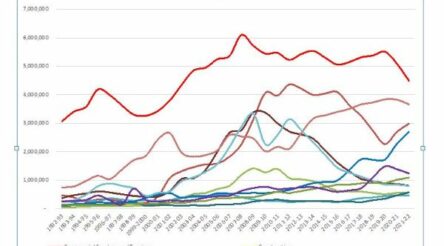
For example, a record level of ransomware attacks are now occurring – an increase greater than the past five years combined globally.
While organisations are now more aware of the reputational and financial risks that ransomware now poses, the sharp increase is a reminder that this method has proven the most effective pathway to financial gain for attackers.
While many of the underlying exploits have remained relatively consistent over the recent years of the report, attackers are still able to make greater gains through social engineering, basic web application attacks, and system intrusion, which in the Asia-Pacific region represented 98 percent of breaches for organisations, according to research.
State-affiliated and nation-state actors with the motive of espionage were common for the Asia Pacific region this year.
However, financially motivated crime is still the number one threat actor, something that has not changed over the 15 years. The use of stolen credentials is also four times more likely to be a method of access than exploiting a vulnerability in this region.
Top cyber threats for manufacturing organisations and how to thwart them
The manufacturing sector is a lucrative target for espionage but is also increasingly targeted by criminals via denial-of-service attacks, credential attacks and ransomware.
Manufacturing, with its hum of machinery churning out the key components that make our modern life possible, continues to be a valued target for cyber espionage – mostly due to recent indiscriminate supply chain attacks, which have become an increased way for malicious actors to gain access to a large and well-resourced target.
However, it has also become a lucrative target for financially motivated criminals looking to make a quick dollar, and in fact, sensitive schematics and trade secrets are twice as likely to be breached in manufacturing breaches than the rest of the industries.
There are a number of important steps businesses can take to lessen the risk associated with cyber-attacks that do not require high-level, skilled workers who are so hard to come by currently.
These are mostly quick and easy things to implement that could make all the difference, and things organisations across all industries should act on as a priority:
- Top of the list for any organisation should be implementing two-factor authentication with any devices and applications and preventing the re-use of any passwords
- The default credentials of the point-of-sale controller and other hardware and software should be changed, and all businesses need to ensure that software updates are installed regularly and promptly
- And attackers are targeting data and holding it hostage, so organisations need to identify, classify and securely handle organisational data in all its forms to help prevent it from being exposed through email or misconfigurations. Importantly, correctly classifying data will inform an impact assessment if the data is stolen/ransomed.
It’s worth taking the time to audit and manage who has access to what accounts and whether they really need access to that account. This is especially useful to limit the impact of brute force and credential stuffing attacks.
With evidence highlighting human error is a dominant trend involved in 13 percent of breaches, it’s also crucial that there is regular security awareness and skills training for all employees.
Human fallibility across the board should be taken into account when considering cybersecurity – it’s not just the domain of high-tech systems.
It’s worth investing significant effort in this aspect, as security is only as good as its least aware employee, and there is a world of cognitive hazards that cybercriminals have at their disposal.
Filling the skills gap will take time, but in the meantime focusing on the main ways cyber attackers will try to gain access to data and systems is possible with limited security teams.
John Hines is the Head of Cyber-Security, Asia Pacific at Verizon Enterprise Solutions where he leads a team delivering cutting edge security solutions to enterprise and government customers across the Asia-Pacific region. John has also held various leadership roles with PwC, Trustwave, and Cybertrust.
Picture: John Hines
Subscribe to our free @AuManufacturing newsletter here.
@aumanufacturing Sections
Analysis and Commentary Awards Defence Manufacturing News Podcast Technology Videos